
When a large number of websites are discovered to have been vulnerable, as is the case with websites running recent versions of Drupal, people need clear and unambiguous advice that you can act on. And so, our clear and unambiguous advice is:
If you have a username and password on a site which has been using Drupal for its content management, you should change that password. You will need to change that password everywhere you use it, not just on the potentially affected sites.
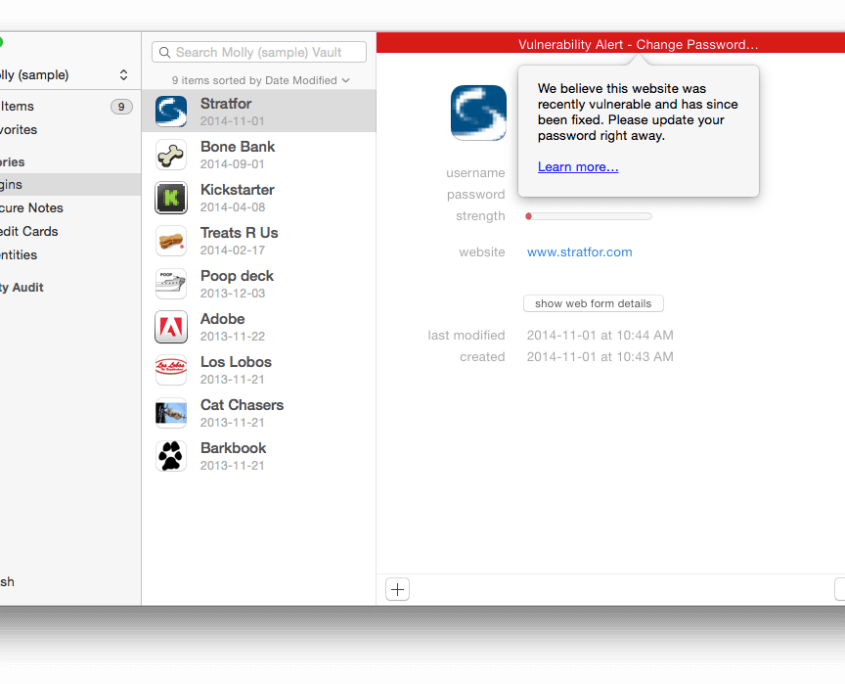
Our Watchtower service within 1Password for Mac and Windows will recommend password changes for a number of sites that we detect as using Drupal. Here you can see what that will look like.
We should also make it clear that none of our systems are affected by the Drupal vulnerability. We don’t use Drupal.
Site administrators know best
We don’t know the status of any particular site other than it appears to be running Drupal. Therefore, if our advice conflicts with advice you received from the administrators of a site, follow their recommendations.
We don’t know when a site gets fixed
Some vulnerable Drupal systems may have been fixed on October 15. Others may still not be fixed yet. Our tests are only capable of determining whether a website is using Drupal (and even that test is imperfect).
Merely patching Drupal is not sufficient for sites that may have been compromised. That is because an attacker using the vulnerability may have left a “backdoor” in a site allowing them back in even after the original vulnerability has been fixed. This makes it yet more difficult to determine whether a site remains vulnerable.
We don’t know if a site has been compromised

Just because a site has been vulnerable doesn’t mean that it has been compromised. However, it appears that automated attacks have been systematically breaking into vulnerable sites and planting “back doors” that would allow the attacker a way back in at any time in the future. So we should assume that most Drupal sites which weren’t patched very quickly on October 15 have been compromised.
A password compromised anywhere must be changed everywhere
If you reuse the same password on more than one site, you will have some extra work cut out for you. Let me explain why.
Suppose that Molly (one of my dogs) has used the same password on Bark Book as she does on Sprayed By a Mink Anonymous, and let’s also suppose that Bark Book gets compromised by Mr Talk (the neighbor’s cat). Molly will need to change her password on both the compromised site (BarkBook.com) and on the uncompromised site (SprayedByMinkAnon.org) . That is because Mr Talk can use what he has learned from Bark Book against all of the sites and services that he thinks that Molly may be using. I must also report that Mr Talk, along with everyone down wind, can easily guess that Molly may well be visiting SprayedByMinkAnon.org.
Molly should take this opportunity to work towards having a unique password for each and every service. 1Password will remember those for her. The closer she gets to having a unique password for each site, the less of a headache the next big incident will be.

 by Jeffrey Goldberg on
by Jeffrey Goldberg on

Tweet about this post