We all witnessed something refreshing last week when MyFitnessPal announced their data breach. They were open and honest about what happened and they should be congratulated.
Many companies hide from the truth and make things much worse for themselves and their customers. Instead, MyFitnessPal did it right. Not only did they handle the disclosure with finesse, they also had excellent systems in place to limit the exposure of the leak.
MyFitnessPal provides a great case study on how to handle a data breach and protect customer information. Let’s start with the announcement itself.
The Announcement
First it needs to be said that it was awesome that there actually was an announcement and that it was published in a timely manner. This is a very good thing!
There was an in-app notification, direct emails, and a pinned Twitter post.


They also posted Frequently Asked Questions that were excellent and when I emailed their support team with some questions for this post, their automated reply included information about the breach and what they were doing to protect their customers.
MyFitnessPal was incredibly open and transparent about everything and at no point did they try to hide details from their users, myself included! That allowed me to update my password and get on with my life.
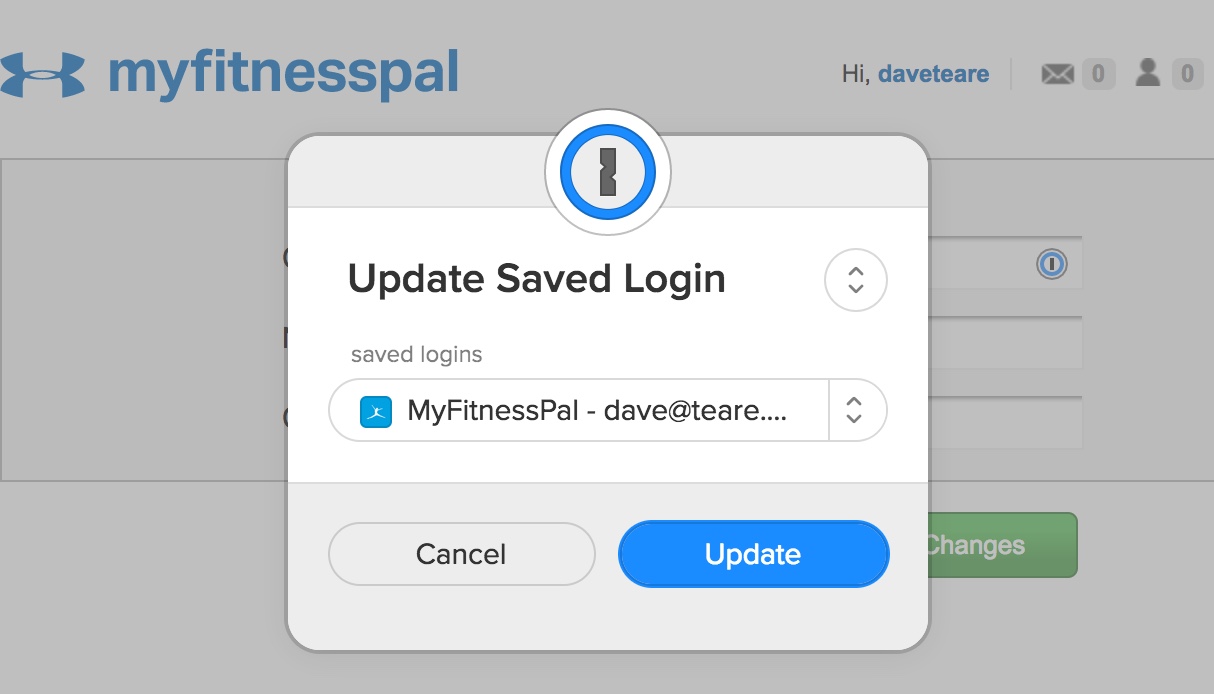
I wasn’t overly attached to qdd84b7UayEwM9J6dZV anyway so I didn’t mind changing it. And since I only used this password on myfitnesspal.com I didn’t need to update any other websites.
Strong unique passwords FTW! 🙂
Secure Handling of Passwords
Equally commendable was how MyFitnessPal stored passwords in their systems. Or more to the point, how they didn’t store passwords.
Many sites choose to store the plain text password, which is bad. The fact that Have I Been Pwned? now has over a half a billion plain text passwords in their database shows how prevalent this horrible bad practice is.
MyFitnessPal was much smarter than that as they never stored the actual password. Instead they stored a hash of the password, most of which were created using bcrypt. Our Chief Defender Against The Dark arts wrote at length about bcrypt and how it can be used to protect user passwords.
It’s possible to go even further than bcrypt and avoid sending passwords to the server by using Secure Remote Password. We use this in 1Password and are quite smitten with it.
Avoiding Other Sensitive Information
The other smart thing MyFitnessPal does that should be commended is collecting and storing the minimum amount of data. From their FAQ:
The affected data did not include government-issued identifiers (such as Social Security numbers and driver’s license numbers) because we don’t collect that information from users. Payment card data was not affected because it is collected and processed separately.
The easiest way to protect data is to not have it in the first place! We follow a similar mentality in 1Password and it’s refreshing to see other companies taking security and privacy seriously.
MyFitnessPal made some excellent design choices and quickly organized an effective response to a bad situation.
For those looking to learn more about the MyFitnessPal breach, Troy Hunt started his Weekly Update 80 with a full discussion on the subject that I found very intriguing, especially the strategy on how to migrate from a SHA-1 hash to using bcrypt.
P.S. A great deal of this post was inspired by an incredible letter I received from Benjamin Fox about how unique passwords helped him quickly recover from the MyFitnessPal breach. Thank you for the inspiration, Benjamin! ❤
Hi Dave,
I know you get hundreds of emails but I can’t help but send this email. I received an email from MyFitnessPal today and of course the news-breaking headlines.
In reading the email, I simply smiled. Headed to my 1password vault and checked the password.
Sure enough, there was a 40 character, numbers + symbols password. I smiled smugly and thought of you.
Your amazing product keeps my data safe every single day. I have not one single duplicated password. Back about 4 years ago I spent the entire weekend updating 200 plus sites with a unique password ( MyFitnessPal being one of them ).
I have recommended so many people to your platform knowing that you have an amazing product and just as importantly, a fantastic support team.
Take care my friend and I send you a warm-hearted thanks from Darwin, Northern Territory, Australia!
Keep doing what you’re doing!
Benjamin Fox.
We really do have the best users in the world. 😘

 by Dave Teare on
by Dave Teare on


Tweet about this post