Only two months ago, in the wake of the “goto fail” bug, we had to point out that 1Password’s security does not depend on SSL/TLS. Today, with the far more damaging Heartbleed bug in OpenSSL, we need to tell you the same. 1Password’s technology is not built upon SSL/TLS in general, and not upon OpenSSL in particular. 1Password’s encryption remains safe.
This bug matters for everyone
Just because 1Password’s technology isn’t affected by this doesn’t mean that you aren’t. Pretty much everyone is affected by this. Many of the secure connections that you use with various services, including HTTPS connections to secure sites for shopping and many other activities, may be fully readable to attackers. Of course, this includes the usernames and passwords that you use to log in to various services. It’s not just HTTPS connections, but IMAPS—how your email program, such as Mail.app or Outlook, talks to a mail server—may be vulnerable.
“So I need to change all my login passwords, right?”
Your 1Password data remains safe, as does your 1Password Master Password. But whether or not you use 1Password to log into an affected site or service, your username and password, along with everything else that happens over that supposedly encrypted connection, may be exposed to attackers.
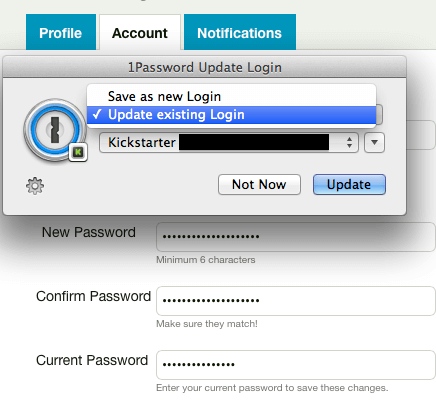
You will, at some point, need to change a lot of passwords. And 1Password makes this much easier than it other would be. But don’t rush to do that just yet. Not every server is affected, and those that are need to fix things at their end before you change your password. If you change your password before the servers fix things, then your new password will also be vulnerable to capture.
All that most of us can do is wait at this point. Presumably, various service providers will announce over the next few days when and whether users should change passwords or be aware that other confidential information may have been exposed.
At this point, I can only guess at how long it will take for various service providers to make announcements. They are in a difficult position right now. First, they need to determine whether they are vulnerable. That means finding out if their particular SSL/TLS service was using OpenSSL (the most popular SSL library in use today) version 1.0.1 (Released March 2012) through 1.0.1f (1.0.1g, containing the fix, was released April 7, 2014).
Once a service upgrades to a fixed version of OpenSSL (or to some other cryptographic library), they will need to revoke the certificate that they had been using with with the vulnerable version of OpenSSL and obtain a new certificate. Exactly how long that takes will depend on how quickly they can get things sorted out with their certification authority. Certification authorities are going to be very busy over the next few weeks.
Only after a new, certified certificate is in place on a server that is not using a broken SSL/TLS library will it make sense for you to update your password for that service (or even trust your communication with it). Most of us simply have to wait until notified by various websites and services when and whether we should change passwords.
Certificates and keys
If you are curious about what is actually exposed by the heartbleed bug, read on. It requires some understanding of how certificates work, but I’ll try to give an overview of just the parts we need for this discussion. I will take a lot of shortcuts in the presentation and pretend that things are simpler than they actually are.
How certificates and keys work
In order for your browser and a web site to encrypt the communication between them, they need to use an encryption key. That key is typically a 128-bit number. Now, it may be that your browser and the particular website have never spoken to each other before, so they need to work out an encryption key for this session in such a way that someone listening in will not know what the key is. It’s as if they have to work out a password to share between them while communicating where anyone can listen.
The encryption key that they work out is just for that particular session. The next time your browser establishes a connection to that server, a new key is worked out. This is called a “session key”.
Establishing a session key
Your browser and the server work out a session key using something called “public key encryption”. Public key encryption is the nearest thing to magic you will find in mathematics and cryptography. When I describe what I do to school kids on career day, I say that I get to think like a criminal and do magic with math.
Anyway, the server will have a public key and a private key that are mathematically related. The public key is not a secret at all. The mathematically related private key is. It is possible to use the public key to encrypt stuff that can only be decrypted with knowledge of the private key.
So (and this is taking a big shortcut), your browser can pick a random session key and encrypt it using the server’s public key. Because only the server knows the corresponding private key, only the server can decrypt the encrypted session key. Once your browser has sent a randomly chosen session key to the server, both the server and browser can use that session key for their communication throughout that session.
The private key is a big, long number. Often thousands of bits long. And it can’t be just anything; it has to have the appropriate mathematical relationship to the public key. Clearly no human is going to be dealing with those keys directly. Typically, those keys are stored in a something that can be used by the server software and is protected by a password.
This scheme of using a password to protect a key and then have the key be used for the encryption is typical of high security software. You find this in SSH, PGP, and in 1Password. A strong key is picked by the software and that key is then encrypted with a password that a human uses. With 1Password, your data is encrypted with a random 256-bit key that is chosen when your data vault is created. Your Master Password is used (indirectly) to encrypt that key (again, I’m skimming over some details).
How heartbleed bleeds your privacy
Anyway, the heartbleed bug pretty much allows an attacker to probe a server that will end up revealing the private key. Once an attacker knows the private key, they can decrypt session keys that have been sent to the server, and thus decrypt all of the encrypted traffic that goes back and forth between the browser and the server.
Another bit of magic with public key encryption is the notion of “digital signature.” Your browser can create a mathematical challenge using the public key that only someone with knowledge of the private key can solve. This is part of how a website proves to a browser that it is what it says it is. If an attacker learns the private key of some website, then it can masquerade as that site.
All in all, the capture of a server’s private key is a bad thing, and that is what this bug enables.
Update for system administrators
Most of us ordinary folk need to wait for sites that need fixing to actually get fixed, then wait for instructions on whether we need to change passwords. But some of us need to get working. The definitive source for information about Heartbleed is heartbleed.com. Since this article was originally written, Filippo Valsorda has published a tool for checking which sites are vulnerable (this has also finally pushed me to play with the Go programming language I’ve been hearing so much about).
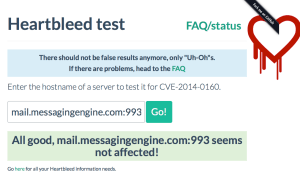
Valsorda has also created a web page based on his testing tool, which makes it easy for people who don’t wish to install and run the command line program to see which websites (or other services) are currently vulnerable to Heartbleed. I wanted to test the IMAP (mail access) server used by Fastmail.fm (which I use for my personal mail). The name of the IMAP server is “mail.messagingengine.com” (which I happened to look up in my Email accounts category in 1Password). Because I wasn’t testing normal HTTPS, which used port 443, I also had to enter the port number for IMAPS, 993. So what I put in the form was “mail.messagingengine.com:993”. This nicely passed the test at the time I tested.
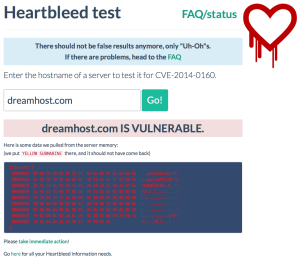
To test a website, you do not need to put in the port number. The test will default to port 443 (HTTPS). So I was able to test Dreamhost.com by just using “dreamhost.com” in the form. At the time I tested, dreamhost had not updated to the fixed version of OpenSSL, and so the test reported it as vulnerable.
Patching OpenSSL isn’t enough
It is important to remember that during the period that your site was vulnerable attackers could have captured the key for the SSL certificate. Once they have your key, they can (under most circumstances) continue to read and manipulate traffic to and from your site. So the next step is to generate a new certificate and get that signed by a Certificate Authority. This is also a good opportunity to ensure that your RSA or DSA key is at least 2048 bits long. 1024 bit RSA and DH keys are no longer considered safe.
Once you have your new certificate signed and in place, you should inform users that their sessions may have been compromised prior to the installation of the new certificate. They should then change their passwords and take whatever other action is appropriate given that confidential data may have been exposed.
Updates
The bulk of this article was drafted late Monday (April 6) night and in the wee hours of Tuesday morning. We will have a series of other articles and announcements coming soon, so please continue to watch the Agile Blog for news here and 1Password on Twitter and Facebook. We will also be providing only minor updates to this post, as we prepare new ones.
April 12
- A new certificate for agilebits.com was put in place on April 10 and Dropbox.com put a new certificate in place on April 11.
- Now that Dropbox is using a new certificate, we’ve removed the earlier advisory for users of the 1PasswordAnywhere feature.
- We’ve added some links to password changing instructions for 1Password 4 for Mac.

 by Jeffrey Goldberg on
by Jeffrey Goldberg on

Tweet about this post