Dropbox has just released a new, optional, two-step authentication process. 1Password 3 (Mac and iOS) and 1Password for Windows use Dropbox for synchronizing your 1Password data across systems and platforms. So anything that has to do with Dropbox security is of interest to us and to 1Password users.
The bottom line is that I recommend 1Password users not be early adopters of this. Early adopters should:
- understand the data security gains and risks thoroughly (discussed below)
- take steps to reduce those risks (have great backups), and
- be very comfortable using pre-release systems
My recommendation does not reflect any criticism of Dropbox’s experimental system. It looks (from my brief exploration) like it is done extremely well. But for the large majority of 1Password users, it’s just a little early to start using their two-step authentication system.
If you would like to know more about the two-step authentication system Dropbox has just rolled out and why I am recommending a “wait-and-see” approach at this point, read on.
Stop trying to scare us away from it. What does it do?
I will return to scaring 1Password users away from jumping on Dropbox’s beta two-step authentication system later in this article. But it will be easier to do so after I’ve outlined how it works. There are also some really cool things about how the protocols for two-factor authentication work, but I will bite my tongue and leave that discussion for another day. What this means, however, is that a great deal of what I say in describing the system below is a pack of lies. I will be describing how things may superficially appear to users, not how it really works.
Dropbox calls their system “two-step verification”, and that is an excellent name for communicating what it does. I will continue to use the term “two-step authentication” because I will need to make use of the more technical term, “authentication”, further on.
Logging in
Once you have set up two-step authentication with Dropbox, then every time you log into Dropbox with a web browser or authorize a new computer or service to use Dropbox, you will be prompted to enter a special six digit code. It will be a different six digit code each time, and the code that you need to enter will be sent to your phone. So in addition needing your Dropbox username and password to connect to Dropbox, you will also need access to your phone.
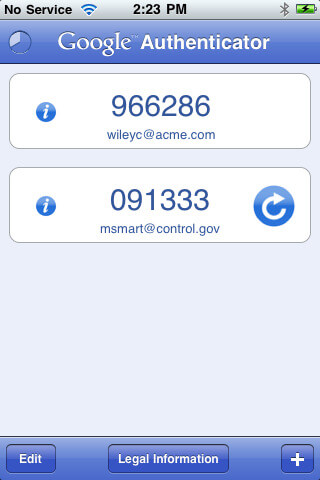
There are a number of ways that Dropbox can send the six digit code to your phone. I have been testing with Google Authenticator, and so far (I’ve only been playing with this for a few hours), it works as advertised and is easy to use.
Already authorized devices
When you first set up Dropbox on your computer or set up 1Password on your iPhone to sync with Dropbox you do not need to authenticate those again. The ability to connect remains until you take specific steps break that link. Enabling two-step authentication doesn’t break those existing links. So if you already have 1Password on your iPhone syncing with Dropbox, you will not need to enter in a six digit code into 1Password to allow that syncing.
Linking new devices
Dropbox has just released a new version of their desktop software which is capable of dealing with their two-step authentication directly. This is great for the desktops, but you might find that you need to download the latest version from Dropbox’s download page. It looks like version 1.4.17 is the first non-beta version that natively supports two-step authentication.
As I mentioned, if you have already set up Dropbox syncing for 1Password on your mobile device it will continue to sync after you turn on Dropbox two-step authentication. If you do need to setup Dropbox syncing from 1Password after you have enabled two-step authentication, there are some additional steps you need to take. I talk about those in a separate section.
What happens when you lose your phone?
The people at Dropbox know full well that people lose access to their phones. It would be terrible if having your phone lost, stolen, or drenched meant that you could no longer get to your Dropbox data. So when you first set up two-step authentication, you will be given a “backup code”. This is a long, random, sixteen character, and impossible-to-remember code. You need to keep this someplace secure because you will need it to reset two-step authentication if you lose your phone.
The obvious place to keep such an important and hard to remember backup code is in 1Password. I set up a Generic Account under Accounts for this and added it as a Note to my Login for Dropbox in 1Password.
Now, suppose you are traveling and your phone gets stolen or damaged. If you don’t have access to a computer or device that is already linked to your Dropbox account, you won’t be able to reset two-step authentication. You won’t be able to access your 1Password data, which in turn means that you won’t be able to access many of the accounts and services you need. At least, you won’t be able to until you either get to the piece of paper where you wrote down your backup code or get to a computer or device that is already linked to your Dropbox account.
Data availability is part of data security
Dropbox’s two-step authentication eliminates one particular risk—someone breaking into your Dropbox account because they’ve discovered your Dropbox password. But it would not, for example, protect against a general Dropbox breach. Also, your 1Password data is already designed to withstand sophisticated attacks if someone does get a copy of it. Thus, the actual security gain for your 1Password data that Dropbox’s two-step authentication adds is minimal. It is of most use to people who have poor password practices and have secret, but unencrypted, data stored on Dropbox.
Data availability is just as much a part of data security as data secrecy. It is the ability to get and use your own data when you need it. For a dramatic case of what it means when people lose access to their own data, consider what happened to Mat Honan. If he had not found a way to get back into his Dropbox account after all of his personal devices and computers were wiped clean, he would have lost all access to his 1Password data.
Because phones can be easily lost, stolen, or damaged, using Dropbox’s two-step authentication increases the risk to data availability. In opting to enable two-step authentication, you are balancing one risk against another. Indeed, most security trade-offs involve balancing one kind of security with another. In this case we are considering a very small gain in protecting data secrecy against a potentially larger, but hard to estimate, risk of losing data availability.
If you insist
If you insist on trying Dropbox’s new two-step authentication process, here are a few recommendations.
1. Be obsessive about data backups
You should have backups of your 1Password data that will:
- be recoverable before you have access to your 1Password data. For example, if your backup is encrypted, you will need a way to get to that password before you have restored your 1Password data
- be recoverable if your house burns down
- be recoverable if your computers and devices are subject to the kind of “remote wipe” attack that Mat Honan experienced
Another way of looking at this is, if you enable two-step authentication, you should not think of Dropbox as a backup system (you shouldn’t anyway for other reasons). I know that I’ve gotten lazier about personal backups since using Dropbox (despite the fact that I shouldn’t). Any such laziness needs to be reversed if you enable tw0-step authentication.
One option is to make a copy of your 1Password data and burn it to a CD. Your 1Password data should include your Dropbox credentials, including the backup code. You may wish to keep a copy of that CD in your car or some location away from your other backups.
2. Write down your Dropbox backup code
Keep copies of the Dropbox rescue or backup code in a variety of places, including on paper. You need this if you lose your phone. And if you lose your phone and have serious loss of access to data on your computers, you will need to reset two-step authentication without having access to what is on Dropbox.
Setting up and using Dropbox’s two-factor authentication with 1Password
To enable Dropbox’s two-step verification, check out this document in their help center.
Once you have set things up and Dropbox is working correctly on your desktops, there is nothing that you need to do with 1Password on your Desktop. 1Password on the desktop doesn’t actually talk to Dropbox; it just makes use of what is in your Dropbox folder.
As I’ve mentioned before, if 1Password on your phones or iPads is already configured to do Dropbox syncing, then again, you are all set to go. Nothing changes. Dropbox has already given a token to the 1Password app which it can use for logging in. It is only if you need to set up Dropbox syncing that you need to take a few extra steps:
Step 1: Follow the normal instructions for setting up Dropbox syncing in 1Password on your device. Note that after you enter your Dropbox username and password, the login attempt will fail.
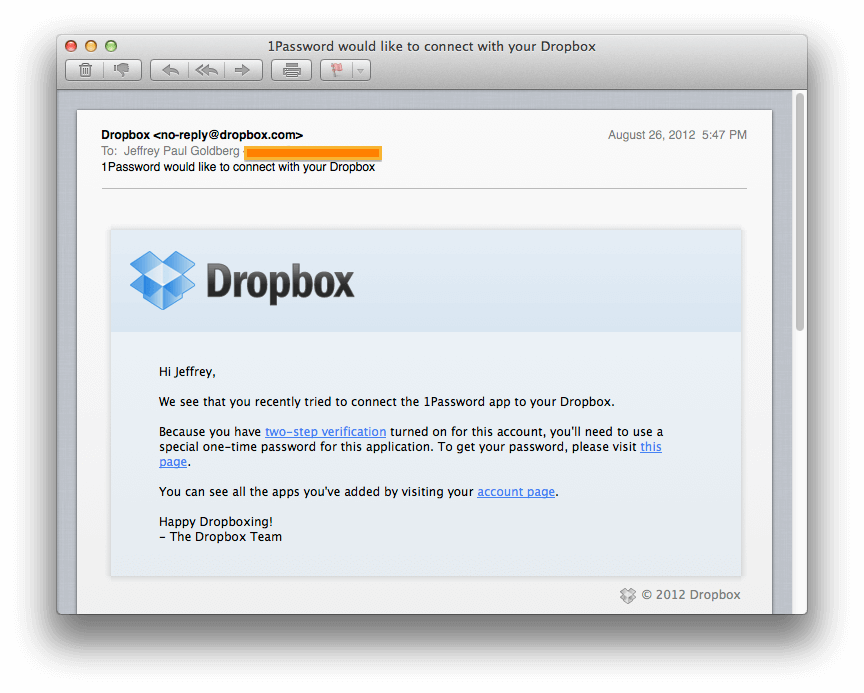
Step 2: Check your email (the email address that is your Dropbox username). You should get some email from Dropbox that looks like this.
Step 3: When you follow the link in that email you will (once you’ve logged onto Dropbox in your web browser) get to a page that looks like this.
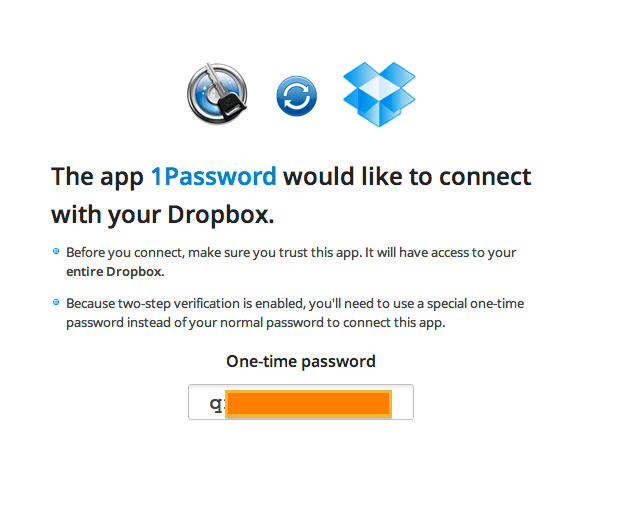
Use the one time password presented on that page as a temporary Dropbox password back in 1Password on your mobile device.
Why am I such a downer?
I am delighted that Dropbox is rolling out a two-step authentication system. This is a good thing for Dropbox to be doing. It is particularly beneficial to those Dropbox users who use the same password for Dropbox as they do at other sites though, naturally, I hope few 1Password users are among them.
It is also early days for this feature. As development and experiences progresses, we will come to better understand the risks of data loss and so be able to provide advice better tuned to the actual risks. But until that time, I have to take the most pessimistic view. I wouldn’t be surprised if weeks from now I’d be encouraging pretty much everyone to sign up.
A note on multi-step authentication and 1Password
Multistep authentication has clear and obvious security benefits. So it is more than natural for people to ask why 1Password doesn’t employ it. I’m planning to write a more detailed explanation of our developing thoughts on that, but I would like to take this opportunity to discuss the difference between authentication and decryption.
When you connect to some service, like Dropbox, you or your system has to prove that it really has the rights to log in as you. That process is called “authentication”. It is the process of proving to the Dropbox servers in this case that you are really you. You can do this through a username and password; you can do this through a username, password, and code sent to your phone; you can do this by having a particular “token” stored on your computer. Authentication always involves (at least) two parties talking to each other. One party (the client) is under your control; the other (the server) is under someone else’s control.
1Password, however, involves the 1Password application (under your control) talking to your 1Password data (under your control) on your local disk (again, under your control). This is not an authentication process. So 1Password doesn’t even do one-step authentication. It does no authentication at all. 1Password doesn’t gain its security through an authentication process. Instead the security is through encryption. Your data on your disk is encrypted. To decrypt it you need your 1Password master password.
There are great advantages to this design: Your data and your decryption of it doesn’t require our participation in any way once you have 1Password. But one disadvantage is that the kinds of techniques used for multi-step authentication are entirely inapplicable to 1Password. Those techniques are designed to add requirements to an authentication process, but unlocking your 1Password data is not an authentication process at all. Because there is no 1Password server, there are no (additional) steps we can insist on as part of a (non-existent) login process.
There are approaches that we could take which would approximate the effect of multi-step authentication for what is actually a decryption process. But I will save discussion of those for another day.
Updated on 8 / 27 to:
- Reflect that Dropbox has fully released two-factor verification. When I was writing this article, it was in “beta”. But at about the same time that this article was first published, Dropbox had released released version 1.4.17.
- Tell fewer lies about how the second step authentication works. It still pretend that data is transmitted to your phone, but I’ve at least toned down that implication.
- In conjunction with Dropbox moving this out of beta and the experience of lots of 1Password users switching over to two-step authentication, I’ve become much more optimistic about when we will feel more comfortable recommending this to 1Password users. I changed my guess of “months” to “weeks”.

 by Jeffrey Goldberg on
by Jeffrey Goldberg on

Tweet about this post